How to Generate Self-signed Certificate in CentOS 7
In this tutorial we will learn how to Generate Self-signed SSL/TLS certificate in CentOS 7. We began by the creating Self signed certificate using the OpenSSL command and we then proceeded to configure Apache HTTPD web server to apply the SSL/TLS certificate.
Prerequisites
You need to have the Apache HTTPD server installed on your CentOS 7 server as well as the mod_ssl package. If the Apache httpd server has not been installed already, install it by following the instructions given in following URL:
How to Install Apache on CentOS 7
Install mod_ssl Apache HTTPD extension module to support TLS/SSL
Apache server needs mod_ssl extension module to be installed to activate SSL support. In CentOS 7, you can install mod_ssl module using the yum command:
yum install mod_ssl
systemctl restart httpdNote that, the mod_ssl package will automatically enable HTTPS for the default web site which you can find under the /var/www/html folder. The default SSL configuration file is /etc/httpd/conf.d/ssl.conf.
How to do it…
Following are the steps we need to follow in order to install Self-signed certificate on CentOS 7 for Apache web server:
- Generate a new SSL/TLS (signed) certificate with OpenSSL command.
- Configure a virtual host to use HTTPS, using the Self-signed certificates.
Generate a new SSL/TLS (signed) certificate with OpenSSL command
We are now ready to begin creating a server certificate. In CentOS 7 we can create a new certificate using openssl command. For example, following openssl command will create a certificate that will valid for 365 days:
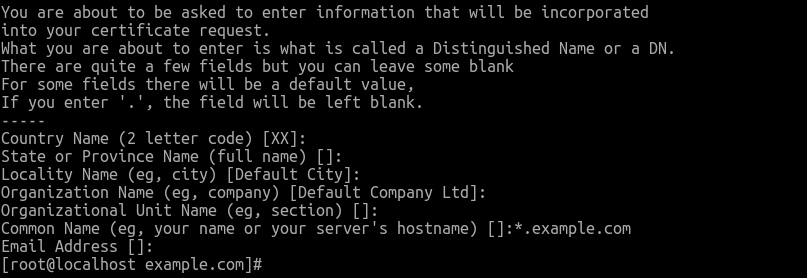
openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/pki/tls/private/example.com.key -out /etc/pki/tls/certs/example.com.crtOnce you run the openssl command, You'll be prompted to enter information for generating the certificate. You leave answer blank to these questions except for the Common Name.
The Common Name value should reflect the domain name of your website. For example, if you want to use this certificate on www.example.com then the Common Name should be www.example.com, if you want to create a wildcard certificate that can apply to all subdomains, then use *.example.com.
The openssl command will create:
- Private Key: The private key, example.com.key will be saved to the /etc/pki/tls/private/ directory (You should not share the private key with anyone).
- Certificate: The example.com.crt will be saved to the /etc/pki/tls/certs/ directory (This is the signed certificate).
Configure a virtual host to use HTTPS, using the Self-signed certificates
We need to configure <VirtualHost> block with the SSLEngine On directive, and configuration for certificates. The following is an example of name-based virtual host for the www.example.com as the website:
<VirtualHost *:443>
ServerName www.example.com
ServerAlias example.com
DocumentRoot /var/www/example.com
ErrorLog "logs/example.com-error_log"
CustomLog "logs/example.com-access_log" combined
SSLEngine on
SSLCertificateFile /etc/pki/tls/certs/example.com.crt
SSLCertificateKeyFile /etc/pki/tls/private/example.com.key
</VirtualHost>You should create a new virtual host configuration file (e.g. example.com-ssl.conf) under the /etc/httpd/conf.d directory.
Generating Self-signed certificate is the easiest way to add TLS encryption to your website. A self-signed certificate is good for tests and internal use. For public access, however, use a certificate from a well-known CA.
Letsencrypt is such a Certificate Authority and you can get a free SSL certificate for your website using the Let's Encrypt.